Deploy with GitHub Actions
Updating from the preview version is not supported. If you deployed the preview version, please proceed with Moving from preview to GA before continuing.
To start, you can either download a copy of the parameter file or clone/fork the repository.
The following changes apply to all scenarios, whether you are aligned or unaligned with ALZ or have a single management group.
Change the value of the following parameters at the beginning of parameter file according to the instructions below:
While it’s technically possible to not add any notification information (no email, no ARM Role, no Logic App, etc.) it is strongly recommended to configure at least one option.Change the value of
enterpriseScaleCompanyPrefixto the management group where you wish to deploy the policies and the initiatives. This is usually the so called “pseudo root management group”, for example, in ALZ terminology, this would be the so called “Intermediate Root Management Group” (directly beneath the “Tenant Root Group”).Change the value of
bringYourownUserAssignedManagedIdentityto Yes if you have an existing user assigned managed identity with the Monitoring Reader role assigned at the pseudo root management group level or leave it to No if you would like to create a new one with the proper rights as part of the deployment process.Change the value of
bringYourownUserAssignedManagedIdentityResourceId. If you set thebringYourownUserAssignedManagedIdentityparameter to Yes, insert the resource id of your user assigned managed identity. If you left it with the default value of No, leave the value blank.Change the value of
userAssignedManagedIdentityNameto a name of your preference. This parameter is used only if thebringYourownUserAssignedManagedIdentityhas been set to No.Change the value of
managementSubscriptionId. If you set thebringYourownUserAssignedManagedIdentityparameter to No, enter the subscriptionId of the management subscription, otherwise leave the default value.Change the value of
ALZMonitorResourceGroupNameto the name of the resource group where the activity logs, resource health alerts, actions groups and alert processing rules will be deployed in.Change the value of
ALZMonitorResourceGroupTagsto specify the tags to be added to said resource group.Change the value of
ALZMonitorResourceGroupLocationto specify the location for said resource group.Change the value of
ALZMonitorActionGroupEmailto the email address(es) where notifications of the alerts (including Service Health alerts) are sent to. Leave the value blank if no email notification is used.Change the value of
ALZLogicappResourceIdto the Logic app resource id to be used as action for the alerts (including Service Health alerts). Leave the value blank if no Logic app is used.Change the value of
ALZLogicappCallbackUrlto the Logic app callback url of the Logic app you want to use as action for the alerts (including Service Health alerts). Leave the value blank if no Logic app is used. To retrieve the callback url you can either use the Get-AzLogicAppTriggerCallbackUrl PowerShell command or navigate to the Logic app in the Azure portal, go to Logic app designer, expand the trigger activity (When an HTTP request is received) and copy the value in the URL field using the 2-sheets icon.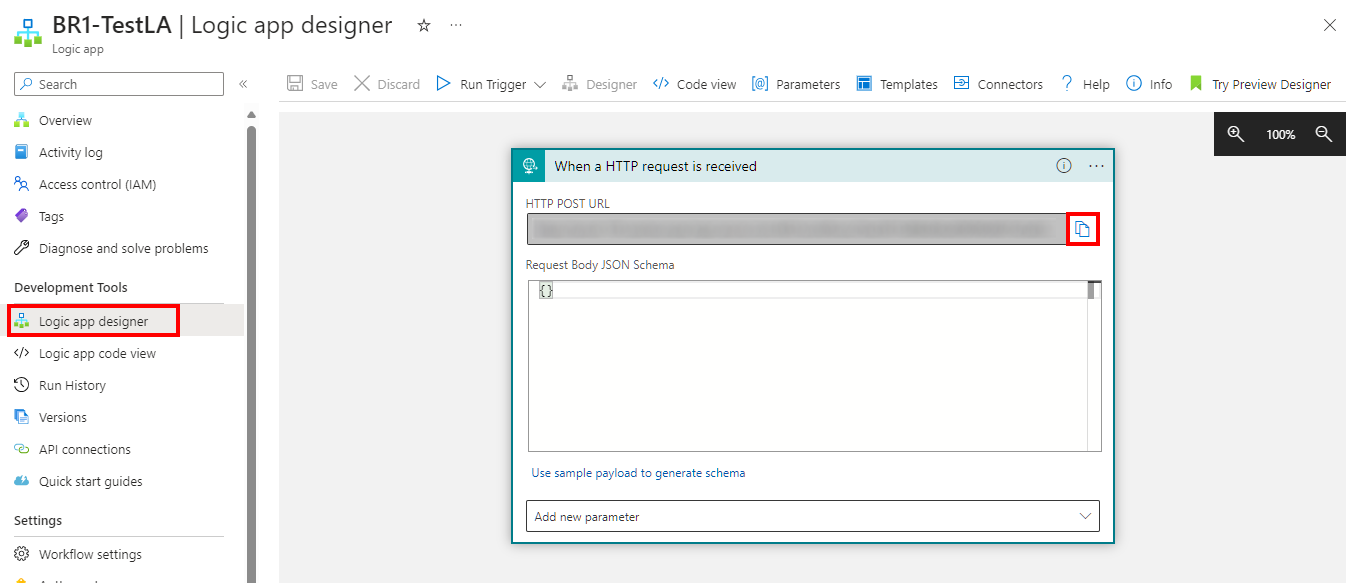
Change the value of
ALZArmRoleIdto the Azure Resource Manager Role(s) where notifications of the alerts (including Service Health alerts) are sent to. Leave the value blank if no Azure Resource Manager Role notification is required.Change the value of
ALZEventHubResourceIdto the Event Hubs to be used as action for the alerts (including Service Health alerts). Leave the value blank if no Event Hubs is used.Change the value of
ALZWebhookServiceUrito the URI(s) to be used as action for the alerts (including Service Health alerts). Leave the value blank if no Webhook is used.Change the value of
ALZFunctionResourceIdto the Function resource id to be used as action for the alerts (including Service Health alerts). Leave the value blank if no Function is used.Change the value of
ALZFunctionTriggerUrlto the Function App trigger url of the function to be used as action for the alerts (including Service Health alerts). Leave the value blank if no Function is used. To retrieve the Function App trigger url with the corresponding code, navigate to the HTTP-triggered functions in the Azure portal, go to Code + Test, select Get function URL from the menu top menu and copy the value in the URL field using the 2-sheets icon.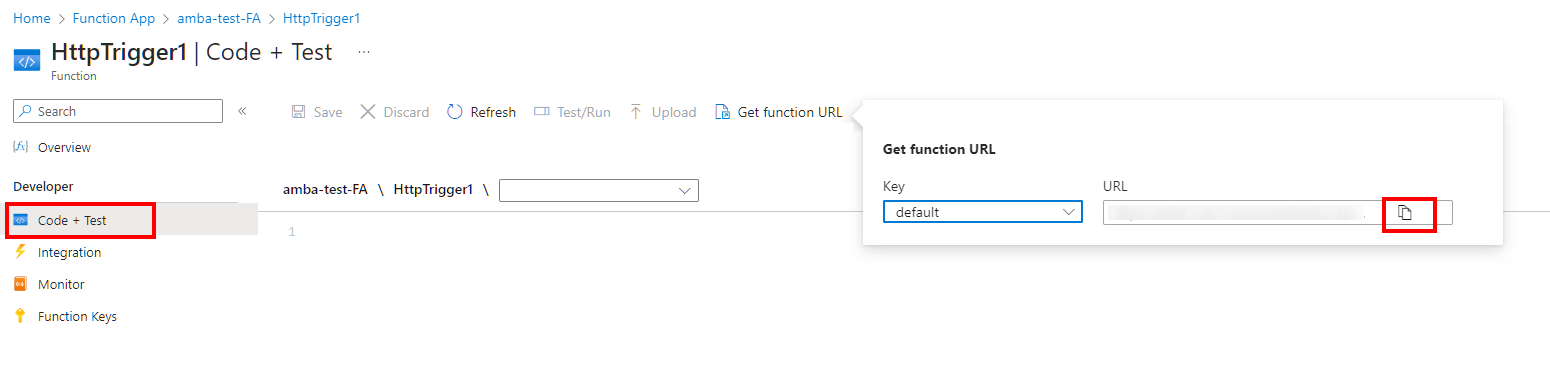
It is possible use multiple email addresses, as well as multiple Arm Roles, Webhooks or Event Hubs (not recommended as per ALZ guidance). Should you set multiple entries, make sure they are entered as single string with values separated by comma. Example:
"ALZMonitorActionGroupEmail": { "value": "action1@contoso.com , action2@contoso.com , action3@contoso.com" }, "ALZArmRoleId": { "value": "8e3af657-a8ff-443c-a75c-2fe8c4bcb635, b24988ac-6180-42a0-ab88-20f7382dd24c" }, "ALZWebhookServiceUri": { "value": "https://webhookUri1.webhook.com, http://webhookUri2.webhook.com" },If you would like to disable initiative assignments, you can change the value on one or more of the following parameters;
enableAMBAConnectivity,enableAMBAIdentity,enableAMBALandingZone,enableAMBAManagement,enableAMBAServiceHealthto “No”.
- Change the value of
platformManagementGroupto the management group id for Platform. - Change the value of
IdentityManagementGroupto the management group id for Identity. - Change the value of
managementManagementGroupto the management group id for Management. - Change the value of
connectivityManagementGroupto the management group id for Connectivity. - Change the value of
LandingZoneManagementGroupto the management group id for Landing Zones.
- Change the value of
platformManagementGroupto the management group id for Platform. The same management group id may be repeated. - Change the value of
IdentityManagementGroupto the management group id for Identity. The same management group id may be repeated. - Change the value of
managementManagementGroupto the management group id for Management. The same management group id may be repeated. - Change the value of
connectivityManagementGroupto the management group id for Connectivity. The same management group id may be repeated. - Change the value of
LandingZoneManagementGroupto the management group id for Landing Zones. The same management group id may be repeated.
For ease of deployment and maintenance we have kept the same variables. For example, if you combined Identity, Management and Connectivity into one management group you should configure the variablesidentityManagementGroup,managementManagementGroup,connectivityManagementGroupandLZManagementGroupwith the same management group id.
- Change the value of
platformManagementGroupto the pseudo root management group id, also called the “Intermediate Root Management Group”. - Change the value of
IdentityManagementGroupto the pseudo root management group id, also called the “Intermediate Root Management Group”. - Change the value of
managementManagementGroupto the pseudo root management group id, also called the “Intermediate Root Management Group”. - Change the value of
connectivityManagementGroupto the pseudo root management group id, also called the “Intermediate Root Management Group”. - Change the value of
LandingZoneManagementGroupto the pseudo root management group id, also called the “Intermediate Root Management Group”.
For ease of deployment and maintenance we have kept the same variables. Configure the variablesenterpriseScaleCompanyPrefix,identityManagementGroup,managementManagementGroup,connectivityManagementGroupandLZManagementGroupwith the pseudo root management group id.
The parameter file shown below has been truncated for brevity, compared to the samples included.
{
"$schema": "https://schema.management.azure.com/schemas/2019-04-01/deploymentParameters.json#",
"contentVersion": "1.0.0.0",
"parameters": {
"enterpriseScaleCompanyPrefix": {
"value": "contoso"
},
"platformManagementGroup": {
"value": "contoso-platform"
},
"IdentityManagementGroup": {
"value": "contoso-identity"
},
"managementManagementGroup": {
"value": "contoso-management"
},
"connectivityManagementGroup": {
"value": "contoso-connectivity"
},
"LandingZoneManagementGroup": {
"value": "contoso-landingzones"
},
"enableAMBAConnectivity": {
"value": "Yes"
},
"enableAMBAIdentity": {
"value": "Yes"
},
"enableAMBALandingZone": {
"value": "Yes"
},
"enableAMBAManagement": {
"value": "Yes"
},
"enableAMBAServiceHealth": {
"value": "Yes"
},
"enableAMBANotificationAssets": {
"value": "Yes"
},
"enableAMBAHybridVM": {
"value": "Yes"
},
"telemetryOptOut": {
"value": "No"
},
"bringYourOwnUserAssignedManagedIdentity": {
"value": "No"
},
"bringYourOwnUserAssignedManagedIdentityResourceId": {
"value": ""
},
"userAssignedManagedIdentityName": {
"value": "id-amba-prod-001"
},
"managementSubscriptionId": {
"value": ""
},
"ALZMonitorResourceGroupName": {
"value": "rg-amba-monitoring-001"
},
"ALZMonitorResourceGroupLocation": {
"value": "eastus"
},
"ALZMonitorResourceGroupTags": {
"value": {
"Project": "amba-monitoring"
}
}
.
.
.
.
}
}
First, configure your OpenID Connect as described here.
To deploy through GitHub actions, refer to the sample-workflow.yml.
If you customized the policies as documented at How to modify individual policies, make sure to modify the workflow file to have the run pointing to your own repository and branch. Example:
run: | az deployment mg create --name "amba-GeneralDeployment" --template-uri https://raw.githubusercontent.com/***YourGithubFork***/azure-monitor-baseline-alerts/***main or branchname***/patterns/alz/alzArm.json --location ${{ env.Location }} --management-group-id ${{ env.ManagementGroupPrefix }} --parameters .\patterns\alz\alzArm.param.json
Modify the following values in amba-sample-workflow.yml:
- Change Location: “norwayeast”, to your preferred Azure region
- Change ManagementGroupPrefix: “alz”, to the pseudo root management group id parenting the identity, management and connectivity management groups
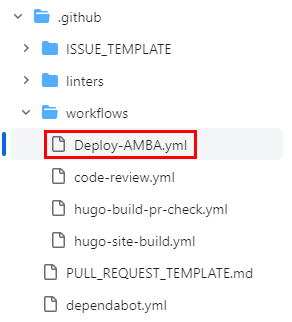
Save the customized amba-sample-workflow.yml in the .github/workflow folder
The file name must perfectly match the name at line 1 of the sample file. You can eventually replace spaces with -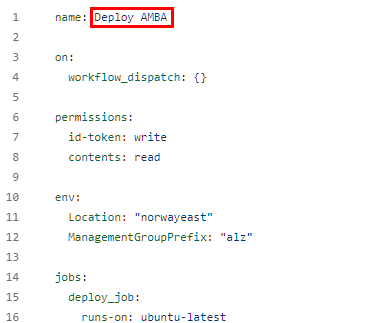
More information about workflow is available in the GitHub documentation at Creating starter workflows for your organization
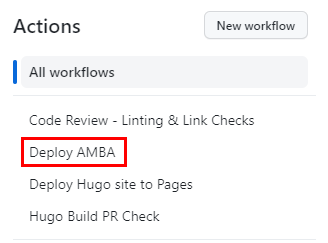
Go to GitHub actions and run the action Deploy AMBA
Above-mentioned “ManagementGroupPrefix” variable value, being the so called “pseudo root management group id”, should coincide with the value of the “parPolicyPseudoRootMgmtGroup” parameter, as set previously within the parameter files.
The location variable refers to the deployment location. Deploying to multiple regions is not necessary as the definitions and assignments are scoped to a management group and are not region-specific.
To remediate non-compliant policies, continue with Policy remediation
